A hash is a fixed-length cryptographic fingerprint generated from block data using algorithms like SHA-256. In blockchain, every block contains the hash of the previous block, creating a tamper-evident chain .If any data changes, the hash changes, invalidating all subsequent blocks. This mechanism makes blockchain ledgers virtually immutable, securing transaction history without the need for a central authority.
How Does a Hash Help Secure Blockchain Technology?
If someone asked you to secure a billion-dollar transaction system with no banks, no central server, and no administrator , how would you do it? The answer blockchain arrived at is elegant: mathematics. Specifically, cryptographic hashing, a mechanism so robust that brute-forcing SHA-256 — the algorithm securing Bitcoin — would theoretically take longer than the current age of the universe, even with every computer on Earth working in parallel (CoinGecko, 2025).
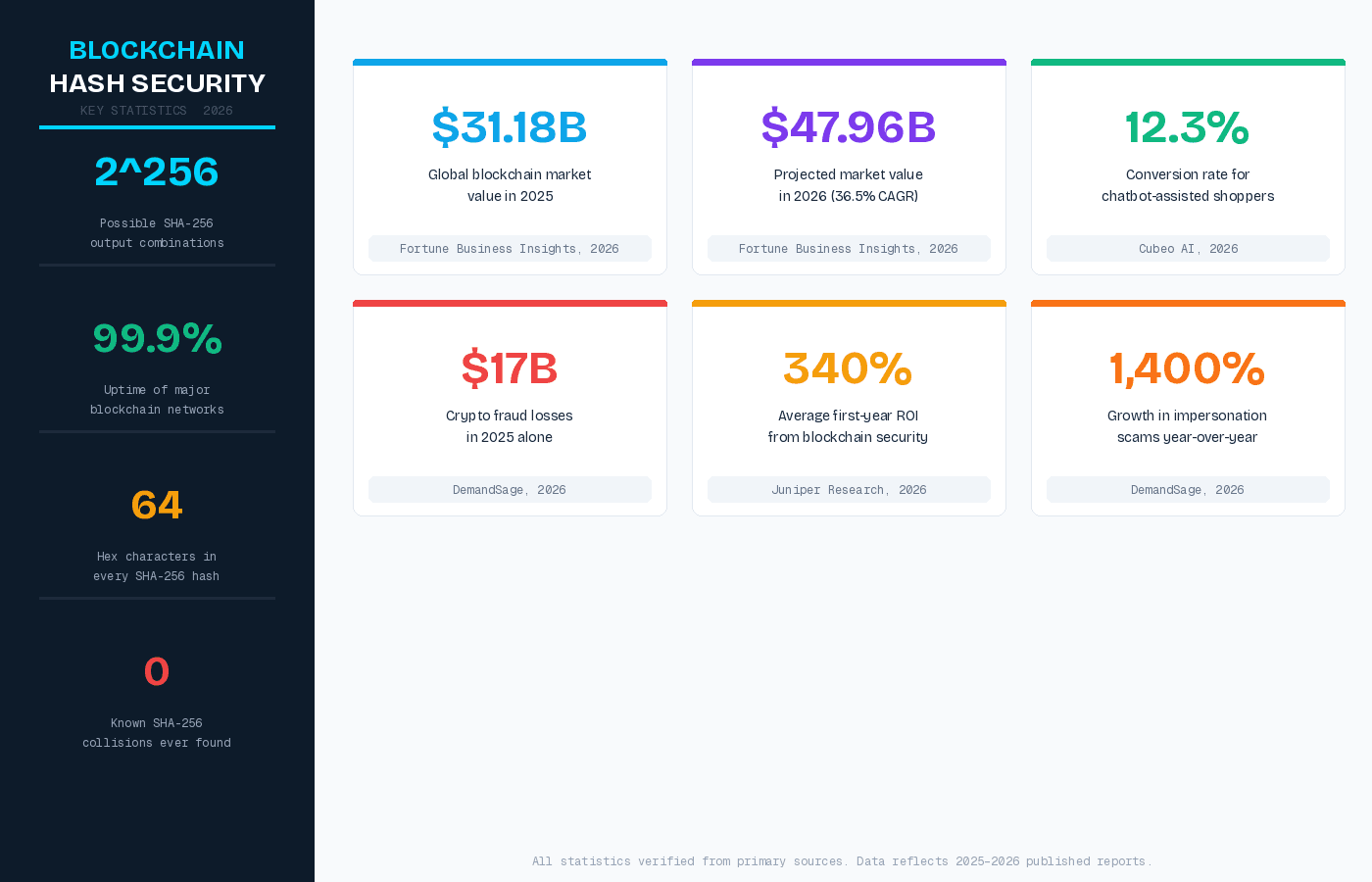
For CTOs evaluating blockchain architecture and developers building decentralized systems, understanding how hashing works isn't just academic. It's the difference between designing a system that genuinely can't be tampered with and one that only appears secure on the surface. In a market now valued at $31.18 billion in 2025 and projected to reach $47.96 billion in 2026 (Fortune Business Insights, 2026), getting the security fundamentals right matters more than ever.
This guide explains exactly what hashing is, how it functions within a blockchain, why its properties make tampering computationally infeasible, and what the evolving threat landscape including quantum computing means for the future of hash-based blockchain security.
What Is a Hash in Blockchain? A Technical Definition
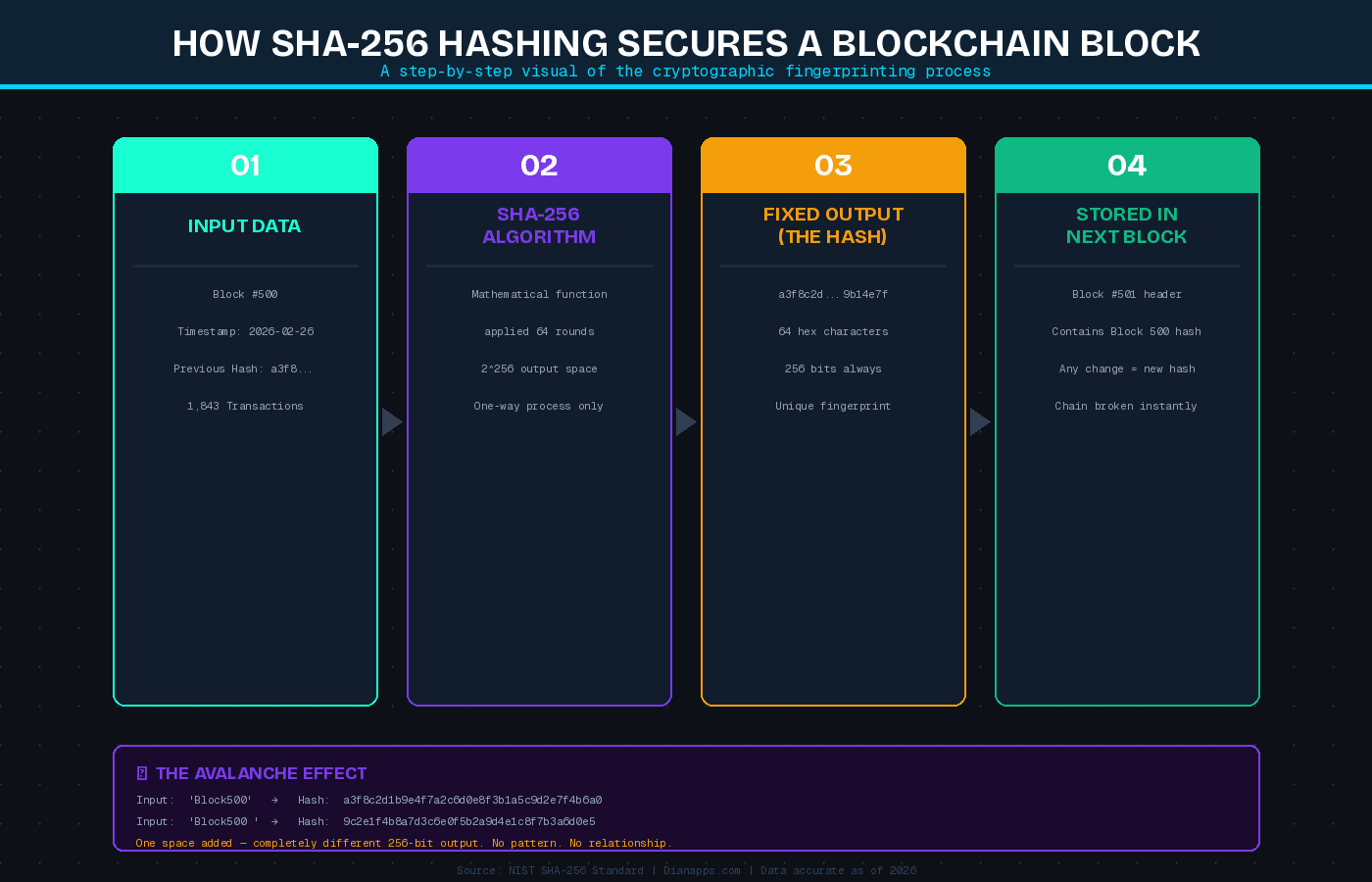
A cryptographic hash function is a mathematical algorithm that takes an input of any size and produces a fixed-length output — called a hash, digest, or fingerprint — that is unique to that specific input. In blockchain technology, this means every transaction, every block of data, and every link in the chain has a corresponding hash that represents it precisely.
SHA-256 (Secure Hash Algorithm 256-bit), developed by the U.S. National Security Agency and published by NIST in 2001, is the hash function powering Bitcoin and many other blockchain networks. It produces a 256-bit output — a 64-character hexadecimal string — regardless of whether the input is a single character or an entire database. The same input will always produce the same hash. A different input — even a single changed character — produces an entirely different hash, with no discernible relationship to the original. This is the avalanche effect, and it's foundational to why hashing works as a security mechanism.
Unlike encryption, hashing is a one-way process. You cannot reverse a SHA-256 hash back to its original input. A 2025 academic study published in the International Journal of Artificial Intelligence confirmed that SHA-256 meets the full reliability and security requirements of production-grade blockchain systems — including pre-image resistance, collision resistance, and deterministic output.
If you’re building a system that leverages these properties, partnering with a professional blockchain app development company ensures your cryptographic architecture from hash algorithm selection to consensus mechanism design is production-ready from day one, not patched together after problems surface.
How Does Hashing Actually Secure a Blockchain?
Hashing secures a blockchain through three interlocking mechanisms. Understanding each one separately makes the overall system much clearer.
1. Block Linking: The Chain Itself
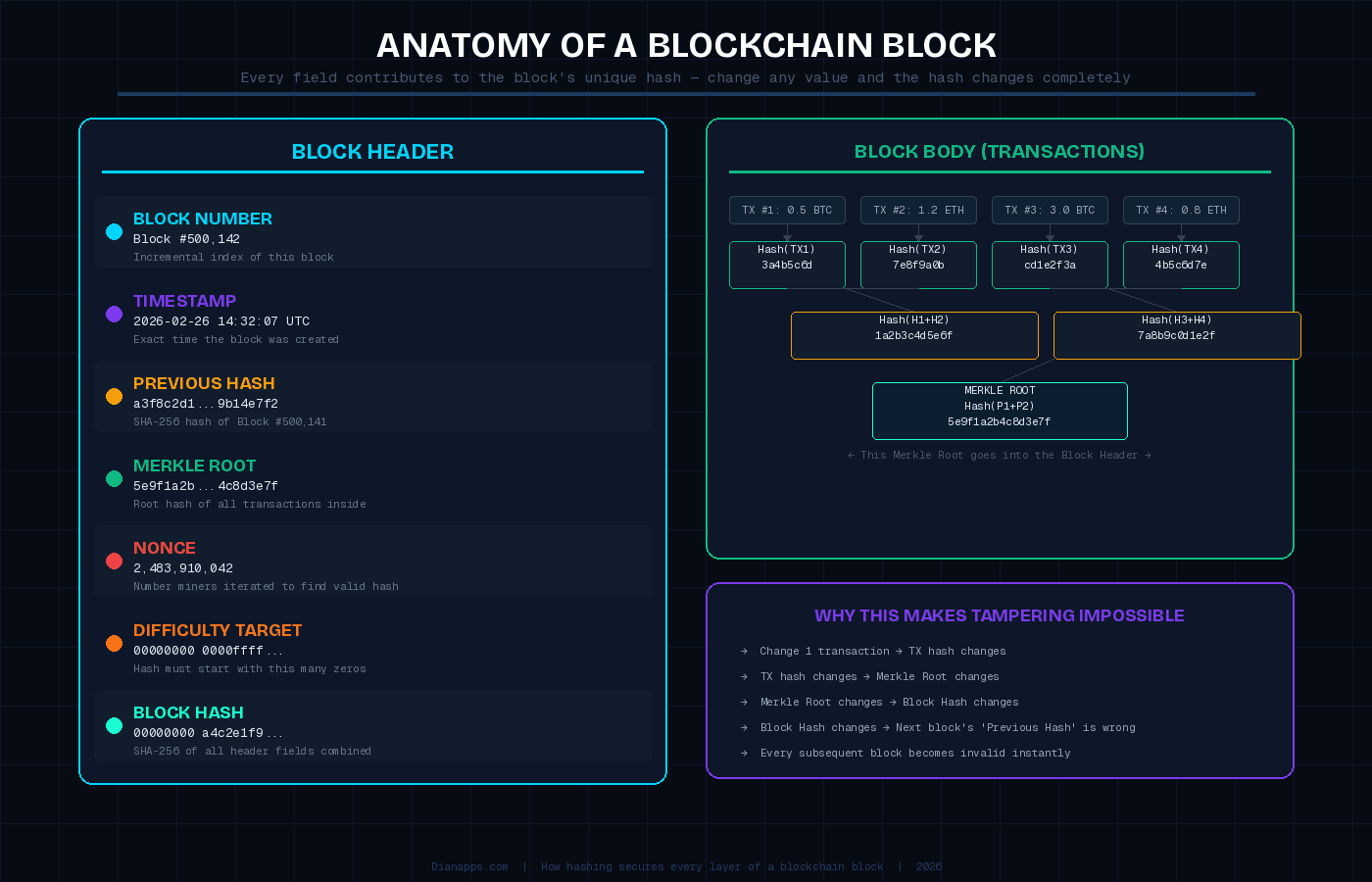
Every block in a blockchain contains, within its header, the hash of the immediately preceding block. This creates a cryptographically enforced sequence — the chain in blockchain. If an attacker tries to alter a transaction in Block 500, the hash of Block 500 changes. That changed hash no longer matches what Block 501 stores as the 'previous block hash,' invalidating Block 501. Fixing Block 501 then invalidates Block 502, and so on, all the way to the most recent block.
To successfully alter historical data, an attacker would need to recalculate the proof-of-work for every block from the altered point forward — faster than the entire honest network is adding new blocks. On the Bitcoin network, that honest network represents an enormous combined computational effort. In practice, this makes rewriting blockchain history computationally infeasible.
2. Merkle Trees: Efficiently Hashing All Transactions
Inside each block, individual transactions are hashed and then organized into a Merkle Tree — a binary tree structure where each parent node is the hash of its two child nodes. The root of this tree, called the Merkle Root, is a single hash that represents every transaction in the block. Any change to any single transaction changes its hash, which cascades up through the Merkle Tree and changes the Merkle Root — immediately signaling that something has been altered, without needing to inspect every transaction individually.
3. Proof of Work: Hashing as Computational Commitment
In Proof of Work blockchains like Bitcoin, miners must find a hash for a new block that falls below a specific target value — a hash that begins with a certain number of zeros. The only way to find this hash is trial and error: miners vary a value called the nonce and repeatedly hash the block header until they hit a valid result. This process — called mining — requires enormous computational effort, making new blocks expensive to produce and therefore expensive to fake. The difficulty adjusts automatically so that a valid block is found roughly every 10 minutes across the whole network, regardless of how much computing power joins or leaves.
To understand how hashing fits within the broader blockchain architecture, our blog on what blockchain and cryptocurrency is all about covers the full system — from distributed nodes to consensus mechanisms — in accessible detail.
The Four Properties That Make Hash Functions Effective for Security
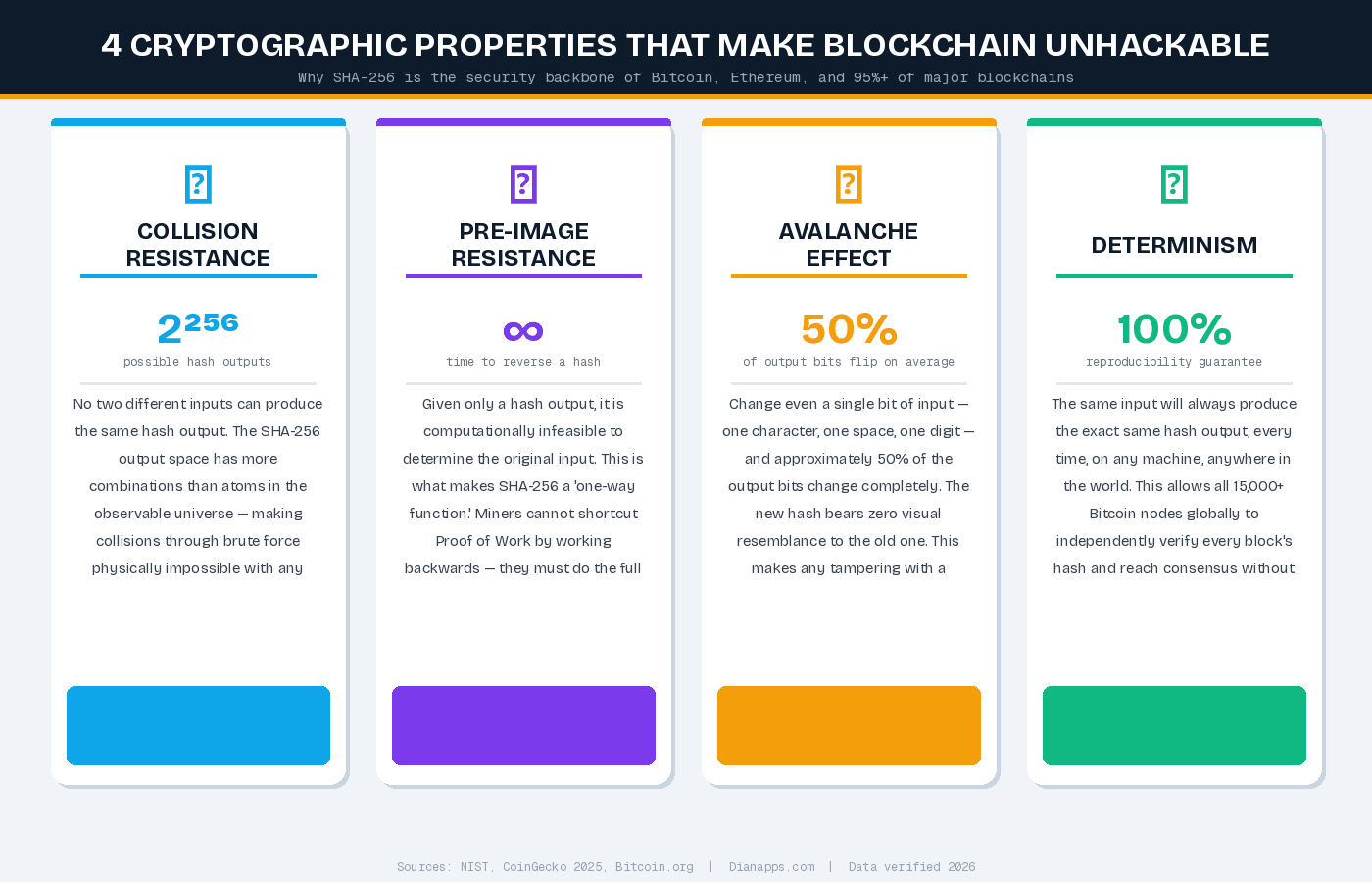
Collision Resistance
No two different inputs should produce the same hash output. For SHA-256, the output space contains 2^256 possible values — a number so large it dwarfs the estimated number of atoms in the observable universe. Finding a collision through brute force is, for all practical purposes, impossible with current and near-future classical computing hardware.
Pre-image Resistance (One-Way Function)
Given a hash output, it should be computationally infeasible to determine the original input. This property protects mining from being shortcutted: miners cannot work backwards from a valid target hash to find an input, so they must do the full computational work of trial and error.
Determinism
The same input always produces the same hash. This allows any node in the network to independently verify a block's hash by hashing the same data themselves. If their result matches the stored hash, the data is intact. If it doesn't, the data has been altered.
The Avalanche Effect
A tiny change to the input — even flipping a single bit — produces a completely different hash output with no resemblance to the original. This property makes any tampering immediately visible. You cannot make a 'small edit' to a block and produce a hash that is only slightly different — the result is an entirely new value, which will fail verification against the stored hash.
Blockchain Security in 2026: What the Data Shows?
The importance of hash-based security scales directly with the value sitting on blockchain networks — and those values are growing at a pace that makes robust security non-negotiable.
The global blockchain technology market was valued at $31.18 billion in 2025 and is projected to reach $47.96 billion in 2026, growing at a CAGR of 36.5% (Fortune Business Insights, 2026). By 2034, projections range from $393 billion (MarketsandMarkets) to over $543 billion (Future Market Insights), with the variance driven by differences in scope — but directional agreement is universal: this market is scaling rapidly.
On the security risk side, the stakes are equally clear. Crypto fraud and scams in 2025 resulted in $17 billion in losses, according to DemandSage (2026), with impersonation scams alone growing 1,400% year over year. This threat landscape makes cryptographic integrity — the kind hash functions provide — not a nice-to-have, but the operational foundation of every trustworthy blockchain.
Quantum computing introduces a longer-horizon concern. Current SHA-256 implementations are not vulnerable to known quantum attacks as of 2026, but NIST and leading blockchain researchers are actively developing post-quantum cryptographic standards. Forward-looking blockchain architectures are beginning to test quantum-resistant hash functions as part of their 2026-and-beyond roadmaps (InnovaraTech, 2026).
Blockchain's applications extend far beyond finance — including securing in-app economies and digital assets. Our blog on how blockchain is revolutionizing in-game economies explores one of the most compelling real-world use cases for immutable hash-backed ledgers today.
Common Misconceptions About Hashing and Blockchain Security
Confusing hashing with encryption. Encryption is reversible — you decrypt it with a key. Hashing is not. A SHA-256 hash cannot be reversed to reveal the original data. They serve different purposes: encryption protects data in transit; hashing verifies data integrity. Treating them interchangeably leads to architecture errors with serious security consequences.
Assuming 'blockchain' means 'unhackable.' Hashing makes blockchain ledger data tamper-evident, not every component of a blockchain system invulnerable. Smart contract vulnerabilities, wallet key management failures, and bridge exploits are real attack surfaces that hashing does not protect against. Security is a full-stack discipline.
Believing SHA-256 will hold indefinitely without review. SHA-256 is secure against classical computing attacks today. But blockchain developers building systems intended to operate for decades should monitor NIST's post-quantum cryptography standardization work and plan for algorithm agility — the ability to swap hash functions without rebuilding the entire system.
Treating Proof of Work as the only valid consensus approach. Hashing secures Proof of Work through computational commitment, but Proof of Stake systems use hashing differently — primarily for block and transaction identification rather than as a mining mechanism. Neither approach is universally superior; the right choice depends on your network's security model, scale, and energy requirements.
Underestimating the 51% attack surface on smaller networks. The security of Proof of Work relies on the cost of controlling 51% of the network's hash rate. On small networks with limited miners, this attack is economically feasible. Hash rate distribution is a genuine security consideration when designing or joining a blockchain network, not just an academic footnote.
Best Practices for Hash-Based Blockchain Security
- Choose the right hash algorithm for your consensus model. Bitcoin uses SHA-256 for Proof of Work. Ethereum uses Keccak-256. Litecoin uses Scrypt. Each has different properties for ASIC resistance, speed, and energy use. The algorithm choice has long-term implications — change it later and you've effectively forked the chain.
- Plan for algorithm agility from day one. As post-quantum cryptography standards mature through NIST's formal process, blockchain systems should be architected so hash functions can be upgraded without full protocol rewrites. Build this flexibility in at the design stage, not in response to a vulnerability disclosure.
- Audit smart contract code separately from chain-level security. Hashing secures the ledger. It does not protect against logic errors in smart contracts running on top of the chain. Engage specialized smart contract auditors before deployment on any production system handling real value.
- Monitor hash rate concentration on your network. For Proof of Work chains, track mining pool concentration. If any single entity controls more than 30–40% of hash rate, the 51% attack risk becomes operationally relevant, not theoretical. Implement monitoring and governance responses before this threshold is reached.
- Use Merkle proofs for efficient verification in large systems. Rather than re-verifying every transaction in a block, Merkle proofs let you verify a specific transaction's inclusion with a logarithmic number of hash comparisons. This is especially important for mobile and lightweight client implementations where bandwidth and compute are constrained.
- Never rely on a single layer of security. Hash-based immutability is the foundation, not the ceiling. Layer it with strong key management, multi-signature wallet requirements, access control on node infrastructure, and incident response plans that don't depend on reversing on-chain transactions — because you can't.
For mobile applications with embedded blockchain functionality, securing the client layer is as important as securing the chain. Our blog on how blockchain enhances mobile app security details the specific integration patterns that CTOs and mobile architects should understand before shipping.
Real-World Scenario: Hash Security in a Supply Chain Blockchain Deployment
Consider a US-based logistics company building a private blockchain to track pharmaceutical shipments across multiple custody points. Each handoff — from manufacturer to distributor to pharmacy — is recorded as a transaction. The concern: any single bad actor in the chain could potentially alter a record to falsify provenance or mask product substitution.
By implementing a SHA-256-based blockchain where each custody event is hashed and linked to the previous one, the system creates an auditable trail where any alteration — even changing a timestamp by one second — produces a hash mismatch that propagates forward through every subsequent block. Regulators and auditors can independently verify the entire chain history without trusting any single party. The Merkle Tree structure inside each block means verifying a specific shipment record requires only a handful of hash comparisons, not inspecting thousands of transactions.
The result is tamper-evident provenance at scale — exactly what pharmaceutical compliance requires — with no central database that can be silently modified. This is hashing doing precisely what it was designed to do.
Conclusion
Cryptographic hashing is the mechanism that transforms a distributed list of transactions into a blockchain — a structure where history genuinely cannot be rewritten without the tampering being immediately detectable. SHA-256's collision resistance, pre-image resistance, determinism, and avalanche effect combine to create a security model that has protected hundreds of billions of dollars in value across Bitcoin, Ethereum, and thousands of other networks since 2009.
For CTOs and blockchain developers building in 2026, the foundational principle holds: get the hash function right, architect for algorithm agility, and treat chain-level immutability as the floor not the ceiling of your security posture. The blockchain market is scaling too fast and carrying too much value for any other approach to be acceptable.
Frequently Asked Questions
Q: What is a hash in blockchain and why does it matter?
A hash in blockchain is a fixed-length cryptographic fingerprint — generated by algorithms like SHA-256 — that uniquely represents a block's data. It matters because every block stores the hash of the block before it, creating a tamper-evident chain. Alter any historical block, and its hash changes, breaking every link in the chain from that point forward and making the tampering immediately detectable across all network nodes.
Q: What hashing algorithm does Bitcoin use, and how secure is it?
Bitcoin uses SHA-256, a 256-bit algorithm developed by the NSA and published by NIST in 2001. Cracking it through brute force would require attempting 2^256 combinations — a number so vast it would take longer than the age of the universe even with every computer on Earth combined (CoinGecko, 2025). As of 2026, there are no known real-world attacks capable of breaking SHA-256. Post-quantum cryptography research continues, but practical quantum threats to SHA-256 remain a future concern, not a present one.
Q: Is hashing the same as encryption in blockchain?
No — they are fundamentally different. Encryption is reversible: you can decrypt data with the right key. Hashing is a one-way function: a SHA-256 hash cannot be reversed to recover the original input. In blockchain, hashing is used to verify data integrity, not to hide data. Confusing the two leads to architectural errors, particularly in systems that need to distinguish between data privacy and data tamper-evidence.
Q: Can quantum computers break blockchain hashing?
Not currently, and not in the near term. SHA-256 is not vulnerable to known quantum attacks as of 2026. Grover's algorithm — the most relevant quantum threat to hash functions — theoretically reduces SHA-256's effective security from 256 bits to 128 bits, which remains computationally infeasible to exploit. However, NIST is actively developing post-quantum cryptographic standards, and forward-looking blockchain architects should design for algorithm agility — the ability to swap hash functions as standards evolve — rather than assuming SHA-256 is permanent.
Q: How does hashing prevent blockchain data from being altered?
Hashing prevents alteration through chain linking and computational cost. Each block contains the hash of the previous block — so altering any historical block changes its hash, which invalidates every subsequent block. To successfully rewrite history, an attacker would need to recalculate proof-of-work for every block from the altered point forward, faster than the entire honest network. On established networks, the computational and economic cost of this makes such an attack practically impossible.








Leave a Comment
Your email address will not be published. Required fields are marked *