Quick Summary:
|
How does a block of data on a blockchain get locked?
So how does a block of data on a blockchain actually get locked? The short answer is: through three processes that work together so tightly that undoing any one of them collapses the whole thing. Let's walk through each one.
Why Does Locking Data Even Matter?
Think about the last time you signed a contract. You signed it, the other party signed it, and then it went into a drawer or a lawyer's office, where nobody could quietly edit it later. The physical signature and the third-party witness were the 'lock.'
Now take that same scenario digital. Two parties agree on something. The record lives in a database. And unless that database has extraordinary protection, someone with the right access can change what it says overnight. That is the fundamental problem that has plagued digital recordkeeping since the beginning of the Internet.
Blockchain's answer is not a better password or a stronger firewall. It is a structural approach one where the data itself becomes the lock. And understanding how that works is what this entire blog is about.
So how does a block of data on a blockchain actually get locked? The short answer is: through three processes that work together so tightly that undoing any one of them collapses the whole thing. Let's walk through each one.
What Is Inside a Block Before It Gets Locked?
You cannot understand how a block gets locked without first understanding what is inside it. Every block on a blockchain carries four core components, and all four play a role in the locking process.
| Component | What it Contains | Why It Matters for Locking |
| Transaction Data | The actual records of payments, contracts, and asset transfers | The content that must stay unchanged forever |
| Timestamp | Exact date and time the block was created | Prevents backdating or replay attacks |
| Previou’s Block’s Hash | A cryptographic fingerprint of the block before it | This is what chains the blocks together |
| Nonce | A number of miners adjust in Proof of Work systems | Used to generate a hash that meets the network's difficulty target |
Notice that the third component of the previous block's hash. That single detail is what turns a database of blocks into a chain. Remove it, and you just have isolated records. Include it, and you have a structure where every block is mathematically dependent on the one before it.
The Three-Layer Process That Locks a Block
Here is where most explanations either oversimplify or go too deep. The truth is right in the middle: three distinct processes run in sequence, and each one does something the others cannot do alone.
Layer 1: Cryptographic Hashing: The Digital Fingerprint
Every block, once assembled, gets fed through a cryptographic algorithm. Bitcoin uses SHA-256. The output is a 64-character string, the block's unique hash that represents everything inside it.
What makes this powerful is a property called the avalanche effect. Change one word in a transaction, change the timestamp by a second, change anything at all, and the hash output changes completely. Not slightly. Completely. It is not a gradual drift. It is a total transformation.
This means the hash is not just an ID. It is a sealed proof that the block's content has not changed since it was created. If the hash still matches, the data is intact. If it does not, something has been altered, and the network knows immediately.
Layer 2: Chain Linkage: Why One Change Breaks Everything
This is the piece that makes blockchain different from every other encrypted database. Each block does not just store its own hash; it stores the hash of the block before it. That creates a direct mathematical dependency between every block in the chain.
Picture it like this: imagine a row of dominoes where knocking one over forces all the others to fall, but in reverse. If you try to change block #400 on Bitcoin's blockchain, its hash changes. That means block #401, which stored #400's original hash, is now pointing to something that no longer exists. Its own hash changes. Block #402 breaks. And so on, all the way to today.
To successfully alter one historic block, you would need to recalculate every single block that came after it across every computer on the network faster than the network is adding new blocks. Bitcoin processes around 600 exahashes per second. That is not a security measure. That is a mathematical wall.
Layer 3: Consensus: The Network Has to Agree
Hashing and chain linkage make tampering detectable. But they do not, by themselves, decide who gets to add the next block. That is what consensus mechanisms do and they are the final gate a block must pass through before it is permanently locked. There are two dominant models in 2026:
Proof of Work (PoW) | Proof of Stake (PoS) | |
| Used by | Bitcoin, Litecoin | Ethereum (post-2022), Solana, Cardano |
| How It Works | Miners race to solve a cryptographic puzzle; the winner adds the block | Validators stake crypto as collateral; selected to verify the next block |
| Block Time | ~10 minutes (Bitcoin) | ~12 seconds (Ethereum) |
| Energy | Very High | ~99.95% lower than PoW |
| Attack Cost | Billions in hardware & electricity | Economic penalty: attacker loses their own staked assets |
Both achieve the same outcome: no single actor can add a block unilaterally. The network decides. And once the network decides, the block is in permanently.
Recommended Read: Understanding The Basics Of Blockchain Technology: A Beginner’s Guide
The Merkle Tree: How Thousands of Transactions Become One Hash
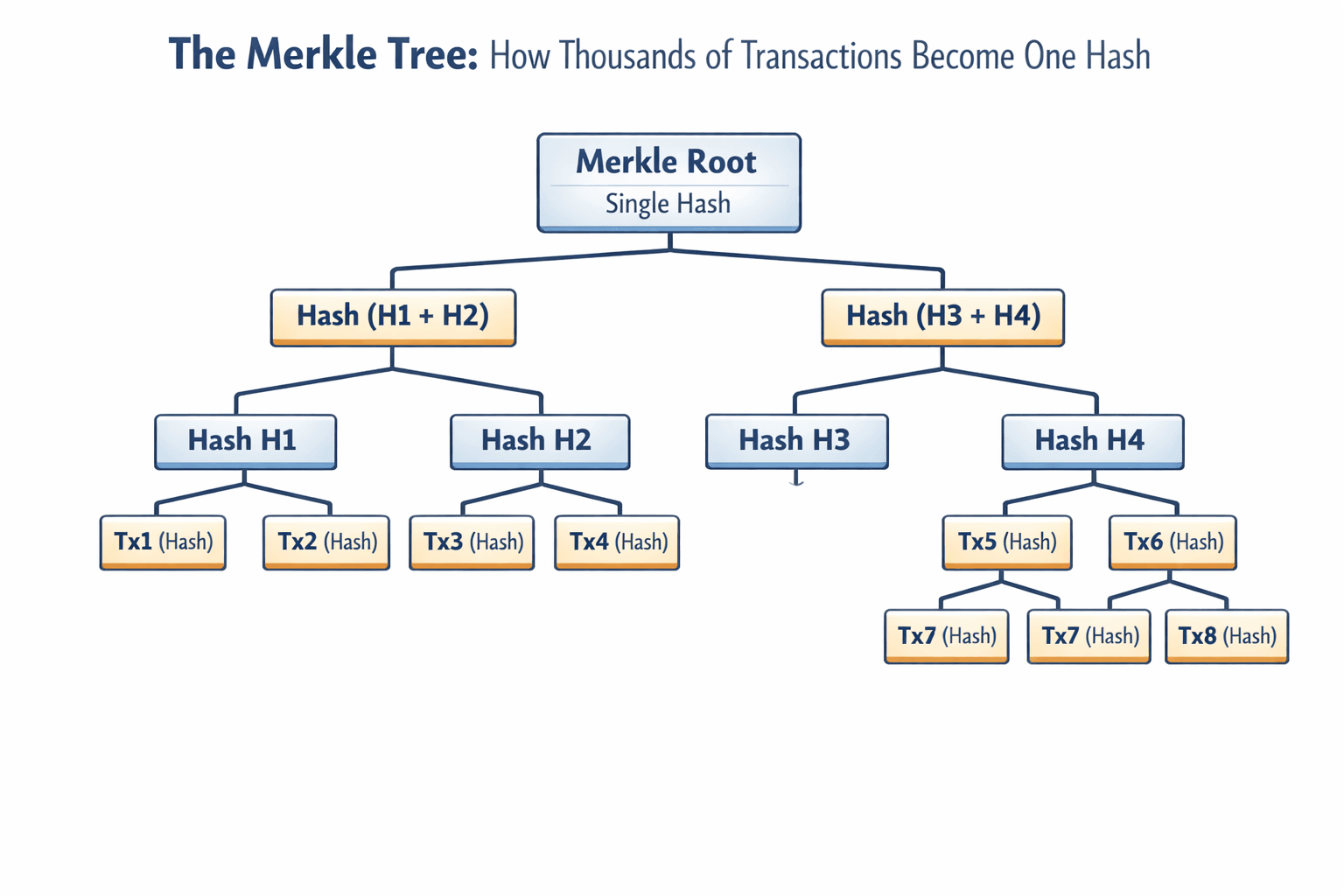
A block can hold thousands of individual transactions. So how does a single hash represent all of them without becoming unreliable? The answer is a data structure called the Merkle Tree, and it is one of the more elegant pieces of engineering behind blockchain.
Every transaction in a block is hashed individually. Those hashes are then paired up and hashed together. Those combined hashes are paired and hashed again. This process repeats until only one hash remains, called the Merkle Root. That root is what gets stored in the block header.
The result: change any single transaction anywhere in the block, and the Merkle Root changes. Which changes the block's hash. Which breaks the chain. One transaction. The whole chain feels it.
Step by Step: What Actually Happens When a Block Gets Locked
Here is the full sequence from the moment a transaction is created to the moment it is sealed into the chain forever.
A Transaction Is Created and Broadcast
A user initiates a transaction, a payment, a smart contract execution, or a data update. It is digitally signed with the sender's private key and broadcast to every node on the network.
Nodes Independently Verify the Transaction
Every node checks: Is the digital signature valid? Does the sender have sufficient balance? Has this transaction been submitted before? Only transactions passing all checks move forward. There is no central authority making this call; every node does it independently.
Verified Transactions Are Grouped Into a Block
Valid transactions are pooled and assembled into a candidate block. The block includes the transaction data, a timestamp, the previous block's hash, and a nonce (in PoW systems). The Merkle Tree is constructed from all included transactions, producing the Merkle Root.
The Block Is Hashed
All of the block's contents are run through a cryptographic hash function. The output of the block's unique hash is its identity and its seal. Any post-hoc change to the block's data will produce a different hash, immediately exposing the tampering.
Consensus Is Reached
In PoW, miners compete to find a nonce that produces a hash meeting the network's difficulty target. The winner broadcasts the solution. Other nodes verify it in milliseconds. In PoS, a validator is selected based on their stake and verifies the block. Either way, the network agrees before anything is finalised.
The Block Is Added and Locked Permanently
Once consensus is reached, the block joins the chain. Its hash is stored in the next block. From this moment, altering this block would require recalculating every subsequent block faster than the entire network, a feat that is not just difficult but economically irrational at any scale.
Recommended Read: The Role of Smart Contracts in Blockchain Development
Digital Signatures: The Lock Before the Lock
Most explanations of block locking skip this part. But digital signatures are actually the first layer of protection; they happen before the block even exists.
When you initiate a transaction, your wallet uses your private key to generate a digital signature unique to that specific transaction. This signature proves two things: (1) you authorised this transaction, and (2) the transaction has not been modified since you signed it. The network uses your public key to verify the signature, but cannot reverse-engineer your private key from it.
This means that by the time transactions reach the block-building stage, they have already been individually authenticated. The block's hash then seals the authenticated set together. It is layers of locks, not a single lock.
Why This Matters: Where Block Locking Is Protecting Real Data Right Now?
This is not theoretical security. According to Market Data Forecast, the block-locking mechanism is expected to protect $34.19 billion worth of blockchain infrastructure by 2026, and the industries relying on it are growing rapidly.
Healthcare: Estonia's Unalterable Patient Records
Estonia secured health records for over 1.3 million citizens using KSI blockchain technology. Every single access to a patient's data is recorded as a locked block creating an immutable audit trail. Patients can see exactly who viewed their information and when. No hospital administrator can quietly edit that log.
Supply Chain: Maersk and the $200 Billion Counterfeit Problem
Global supply chains lose billions annually to counterfeit goods and documentation fraud. Maersk's blockchain-based logistics platform records every handoff in a product's journey as a locked block. If someone tries to insert a fraudulent entry, a fake customs stamp, or a forged certificate of origin, the chain breaks and the fraud is exposed.
Finance: Real-Time Settlement With an Immutable Trail
JPMorgan's Onyx platform, Ripple's payment network, and a growing number of central bank digital currency (CBDC) pilots now rely on blockchain's locked ledger for interbank settlements. Over 137 countries are currently exploring CBDCs, with China's digital yuan and India's e-rupee already in active circulation. The reason they trust blockchain for sovereign-level finance is the same reason enterprises do: once locked, the record cannot be changed by anyone.
Digital Identity: A Record No One Can Forge
77% of business executives believe blockchain will be a disruptive force in their industry, according to a Deloitte global survey, and digital identity is one of the top cited use cases. Estonia's eID system, built on blockchain, allows citizens to vote, bank, and access healthcare using a digital identity no one can forge or retroactively alter. That is the block-locking mechanism, applied to personhood.
The Lock That Runs on Mathematics, Not Trust
Every security system ever built has relied, at some level, on trusting a person. A bank vault relies on the integrity of its staff. A government database relies on its administrators. A signed contract relies on both parties acting in good faith.
Blockchain's block-locking mechanism is the first system in history that removes that dependency entirely. The hash does not care who you are. The chain does not care how much money you have. The consensus mechanism does not negotiate. Once a block is locked, the mathematics holds, and the only way to break it is to outrun the entire network simultaneously.
For businesses looking to implement this level of trustless security, partnering with a blockchain app development company can help design and deploy decentralized applications that leverage these cryptographic principles for secure and transparent digital systems.
In a world where over 80% of Fortune 500 companies have adopted blockchain in some form, and where governments are building national identity systems on it, that mathematical certainty is not just impressive. It is the whole point.
Frequently Asked Questions
How does a block of data on a blockchain get locked?
Through cryptographic hashing, chain linkage, and network consensus, three processes work together to make altering any locked block computationally and economically impossible.
What is the role of a hash in locking a blockchain block?
It's the block's unique digital fingerprint. Change even one character inside the block and the hash changes completely, exposing tampering instantly across the entire chain.
Can a locked block on a blockchain ever be changed?
Practically, no. You'd need to recalculate every subsequent block's hash while simultaneously outpacing Bitcoin's 600 exahashes per second. Technically possible, economically irrational.
What is the difference between hashing and encryption in blockchain?
Encryption is a two-way process that can be unscrambled. Hashing is one-way and irreversible. Blockchain uses hashing because the goal is verification, not secrecy.
What is a nonce in blockchain, and how does it relate to locking?
A nonce is a number miners repeatedly adjust until the block's hash meets the network's difficulty target. Finding it proves the computational work required to lock the block.








Leave a Comment
Your email address will not be published. Required fields are marked *